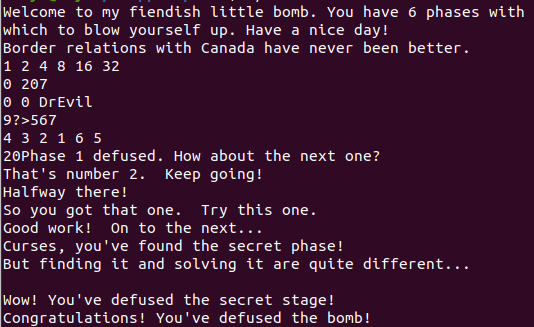
前言:看了好久的书,写了好几个晚上,参考了一些大佬的笔记,终于把这个bomblab写完了
这个著名的bomblab为我们提供了一个二进制文件,然后我们需要将这个二进制文件进行反汇编得到一堆的汇编文件,通过阅读汇编文件中的代码以及GDB的调试来得到需要输入的字符密码来进入下一关。
整个实验一共有六个正式关卡,一个隐藏关卡,密码和进入隐藏关卡的方法也藏在文件中,需要我们一点点的探寻其中的蛛丝马迹,拆开炸弹。如果拆弹失败的话,实验文件会给我们打印出一个BOMB!!!如果你是CMU的学生,每次不小心的BOMB还会扣你这个实验的分数,不过我们不是CMU的学生,就随便他炸了23333
没有实验文件的需要先到这个网站 下载一个
首先我们需要进入到这个lab的文件所在的文件夹下,可以看到有README、bomb、和bomb.c三个文件,我们先打开bomb.c看看有些什么东西
可以看到有6个phase,每个phase基本都是要我们输入一段字符,然后它调用了判断我们字符对不对的函数。大概浏览一下,知道要干什么之后先把bomb文件反汇编一下:
1 objdump bomb -d > disassemble.txt
得到了bomb的反汇编代码打开
看到一堆莫名其妙的东西,不知道怎么下手,想起来之前有6个phase,于是就搜索了下phase,找到了phase所在地,就用GDB来进行调试了
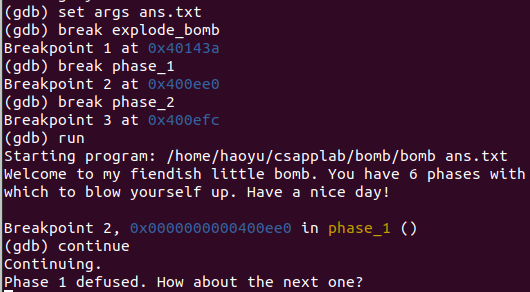
然后给爆炸和phase_1先打上断点
1 2 b explode_bomb b phase_1
run了之后,随便输入一点字符进入phase_1,先把当前的函数用disas指令反汇编一下
不熟悉GDB调试的可以参考CMU的课程提供的手册
phase1的反汇编代码如下
1 2 3 4 5 6 7 8 9 Dump of assembler code for function phase_1: => 0x0000000000400ee0 <+0>: sub $0x8,%rsp 0x0000000000400ee4 <+4>: mov $0x402400,%esi 0x0000000000400ee9 <+9>: callq 0x401338 <strings_not_equal> 0x0000000000400eee <+14>: test %eax,%eax 0x0000000000400ef0 <+16>: je 0x400ef7 <phase_1+23> 0x0000000000400ef2 <+18>: callq 0x40143a <explode_bomb> 0x0000000000400ef7 <+23>: add $0x8,%rsp 0x0000000000400efb <+27>: retq
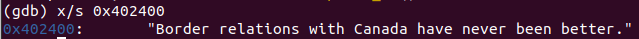
在第二行我们看到了个很奇怪的地址0x402400先把它移动到了esi里,有使用了一个判断字符是否相等的函数,所以我们可以大胆推测密码应该就在0x402400里,直接展示这个地址里的数据:
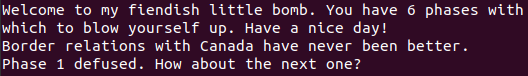
猜的差不多,我们再run一次,这次直接把上面的字符粘贴进去:
发现已经通过了第一关
注意:在每个lab里,每个使用到了固定地址的都很重要,一般都要打印出来看看是个啥
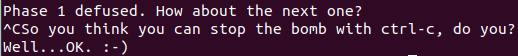
hhh在这里还发现了点彩蛋
现在我们已经有了第一关的密码,所以我们先把它存到一个文档里,然后进入gdb,设置好断点后设置一下命令参数,然后run一波,可以看到我们已经过了第一个phase
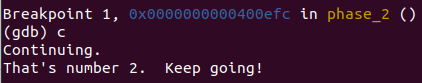
接下来我们开始解决phase2,随便输入一点参数后进入phase2,phase2的反汇编代码如下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 0000000000400efc <phase_2>: 400efc: 55 push %rbp 400efd: 53 push %rbx 400efe: 48 83 ec 28 sub $0x28,%rsp # 堆栈操作 400f02: 48 89 e6 mov %rsp,%rsi 400f05: e8 52 05 00 00 callq 40145c <read_six_numbers> # 读入6个数字 400f0a: 83 3c 24 01 cmpl $0x1,(%rsp) 400f0e: 74 20 je 400f30 <phase_2+0x34> # 堆栈顶部数字 != 1 爆炸 400f10: e8 25 05 00 00 callq 40143a <explode_bomb> 400f15: eb 19 jmp 400f30 <phase_2+0x34> 循环体: { 400f17: 8b 43 fc mov -0x4(%rbx),%eax # %eax = %rsp 400f1a: 01 c0 add %eax,%eax # (%eax) += (%eax) 400f1c: 39 03 cmp %eax,(%rbx) # %eax == valueat(%rsp+4) 400f1e: 74 05 je 400f25 <phase_2+0x29> 400f20: e8 15 05 00 00 callq 40143a <explode_bomb> 400f25: 48 83 c3 04 add $0x4,%rbx # %rbx += 4 #地址+4,相当于移向下一个数 400f29: 48 39 eb cmp %rbp,%rbx # %rbx == %rsp+24#rbx是否为第六个数后的地址 400f2c: 75 e9 jne 400f17 <phase_2+0x1b> } 400f2e: eb 0c jmp 400f3c <phase_2+0x40> 400f30: 48 8d 5c 24 04 lea 0x4(%rsp),%rbx # %rbx = %rsp+4 #rbx存储的应该是地址 400f35: 48 8d 6c 24 18 lea 0x18(%rsp),%rbp # %rbp = %rsp+24 400f3a: eb db jmp 400f17 <phase_2+0x1b> 400f3c: 48 83 c4 28 add $0x28,%rsp 400f40: 5b pop %rbx 400f41: 5d pop %rbp 400f42: c3 retq
这段代码比较长,仔细看可以看出来第一次判断的数字一定是1,需要六个数字,然后每次判断的数字都是前一个数字的两倍,于是我们就可以推导出来答案是1 2 4 8 16 32
phase3的代码稍微有点长
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 0000000000400f43 <phase_3>: 400f43: 48 83 ec 18 sub $0x18,%rsp 400f47: 48 8d 4c 24 0c lea 0xc(%rsp),%rcx 400f4c: 48 8d 54 24 08 lea 0x8(%rsp),%rdx 400f51: be cf 25 40 00 mov $0x4025cf,%esi 400f56: b8 00 00 00 00 mov $0x0,%eax 400f5b: e8 90 fc ff ff callq 400bf0 <__isoc99_sscanf@plt> 400f60: 83 f8 01 cmp $0x1,%eax 400f63: 7f 05 jg 400f6a <phase_3+0x27> 400f65: e8 d0 04 00 00 callq 40143a <explode_bomb> 400f6a: 83 7c 24 08 07 cmpl $0x7,0x8(%rsp) 400f6f: 77 3c ja 400fad <phase_3+0x6a> 400f71: 8b 44 24 08 mov 0x8(%rsp),%eax 400f75: ff 24 c5 70 24 40 00 jmpq *0x402470(,%rax,8) 400f7c: b8 cf 00 00 00 mov $0xcf,%eax 400f81: eb 3b jmp 400fbe <phase_3+0x7b> 400f83: b8 c3 02 00 00 mov $0x2c3,%eax 400f88: eb 34 jmp 400fbe <phase_3+0x7b> 400f8a: b8 00 01 00 00 mov $0x100,%eax 400f8f: eb 2d jmp 400fbe <phase_3+0x7b> 400f91: b8 85 01 00 00 mov $0x185,%eax 400f96: eb 26 jmp 400fbe <phase_3+0x7b> 400f98: b8 ce 00 00 00 mov $0xce,%eax 400f9d: eb 1f jmp 400fbe <phase_3+0x7b> 400f9f: b8 aa 02 00 00 mov $0x2aa,%eax 400fa4: eb 18 jmp 400fbe <phase_3+0x7b> 400fa6: b8 47 01 00 00 mov $0x147,%eax 400fab: eb 11 jmp 400fbe <phase_3+0x7b> 400fad: e8 88 04 00 00 callq 40143a <explode_bomb> 400fb2: b8 00 00 00 00 mov $0x0,%eax 400fb7: eb 05 jmp 400fbe <phase_3+0x7b> 400fb9: b8 37 01 00 00 mov $0x137,%eax 400fbe: 3b 44 24 0c cmp 0xc(%rsp),%eax 400fc2: 74 05 je 400fc9 <phase_3+0x86> 400fc4: e8 71 04 00 00 callq 40143a <explode_bomb> 400fc9: 48 83 c4 18 add $0x18,%rsp 400fcd: c3 retq
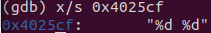
阅读下来看到第四行有个奇怪的地址0x4025cf,不管三七二十一先把它打印出来看看:
可以看出来题目需要我们输入两个整数
继续往下读,看到它使用了一个好像是库函数的函数<__isoc99_sscanf@plt>搜了一下得知它的返回数字为读入的数字数目
接下来就是比较了一下我们输入的第一个数字是否大于7,然后跳转到0x402470+8*%rax的位置,此时我们rax有0~7一共八种选择,所以我们打印一下0x402470附近的地址:
1 2 3 4 5 (gdb) x/8a 0x402470 0x402470: 0x400f7c <phase_3+57> 0x400fb9 <phase_3+118> 0x402480: 0x400f83 <phase_3+64> 0x400f8a <phase_3+71> 0x402490: 0x400f91 <phase_3+78> 0x400f98 <phase_3+85> 0x4024a0: 0x400f9f <phase_3+92> 0x400fa6 <phase_3+99>
再对照代码中的逻辑可以知道按照以下任意一对数字输入都可以通过
数字1
0
1
2
3
4
5
6
7
数字2
207
311
707
256
389
206
682
327
接下来我们就进入到了phase_4,它的反汇编代码如下:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 Dump of assembler code for function phase_4: => 0x000000000040100c <+0>: sub $0x18,%rsp 0x0000000000401010 <+4>: lea 0xc(%rsp),%rcx # %rcx = %rsp + 12 0x0000000000401015 <+9>: lea 0x8(%rsp),%rdx # %rdx = %rsp + 8 0x000000000040101a <+14>: mov $0x4025cf,%esi # 0x4025cf: "%d %d" 0x000000000040101f <+19>: mov $0x0,%eax 0x0000000000401024 <+24>: callq 0x400bf0 <__isoc99_sscanf@plt> 0x0000000000401029 <+29>: cmp $0x2,%eax 0x000000000040102c <+32>: jne 0x401035 <phase_4+41> 0x000000000040102e <+34>: cmpl $0xe,0x8(%rsp) # (%rsp+8) <= 14 0x0000000000401033 <+39>: jbe 0x40103a <phase_4+46> 0x0000000000401035 <+41>: callq 0x40143a <explode_bomb> 0x000000000040103a <+46>: mov $0xe,%edx # %edx = 14 0x000000000040103f <+51>: mov $0x0,%esi # %esi = 0 0x0000000000401044 <+56>: mov 0x8(%rsp),%edi # %edi = %rsp + 8 0x0000000000401048 <+60>: callq 0x400fce <func4> 0x000000000040104d <+65>: test %eax,%eax 0x000000000040104f <+67>: jne 0x401058 <phase_4+76> # 返回值%rax一定为0 0x0000000000401051 <+69>: cmpl $0x0,0xc(%rsp) 0x0000000000401056 <+74>: je 0x40105d <phase_4+81> # (%rsp + 12) == 0 0x0000000000401058 <+76>: callq 0x40143a <explode_bomb> 0x000000000040105d <+81>: add $0x18,%rsp 0x0000000000401061 <+85>: retq
第四行出现了一个地址,打印之后得到的是# 0x4025cf: "%d %d"说明需要我们输入两个整数,然后继续往下读,在倒数第四行可以看出来我们要输入的一个数字一定为0。func4具体的内容还不清楚,把func4的代码输出一下:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 Dump of assembler code for function func4: => 0x0000000000400fce <+0>: sub $0x8,%rsp 0x0000000000400fd2 <+4>: mov %edx,%eax # %eax = 14 0x0000000000400fd4 <+6>: sub %esi,%eax # %eax -= %esi = 14-0 = 14 0x0000000000400fd6 <+8>: mov %eax,%ecx # %ecx = %eax = 14 0x0000000000400fd8 <+10>: shr $0x1f,%ecx # %ecx>>31 = 0//%ecx = sign of %eax 0x0000000000400fdb <+13>: add %ecx,%eax # %eax += %ecx = 14 0x0000000000400fdd <+15>: sar %eax # %eax>>1 // %eax = 7 0x0000000000400fdf <+17>: lea (%rax,%rsi,1),%ecx # %ecx = %rax+%rsi = 7+0=7 0x0000000000400fe2 <+20>: cmp %edi,%ecx 0x0000000000400fe4 <+22>: jle 0x400ff2 <func4+36> # %edi = %ecx 0x0000000000400fe6 <+24>: lea -0x1(%rcx),%edx # %edx = %rcx-1 0x0000000000400fe9 <+27>: callq 0x400fce <func4> 0x0000000000400fee <+32>: add %eax,%eax # %eax = 2*%eax 0x0000000000400ff0 <+34>: jmp 0x401007 <func4+57> 0x0000000000400ff2 <+36>: mov $0x0,%eax # %eax = 0 0x0000000000400ff7 <+41>: cmp %edi,%ecx # %ecx >= %edi? 0x0000000000400ff9 <+43>: jge 0x401007 <func4+57> 0x0000000000400ffb <+45>: lea 0x1(%rcx),%esi # %esi = %rcx+1 0x0000000000400ffe <+48>: callq 0x400fce <func4> 0x0000000000401003 <+53>: lea 0x1(%rax,%rax,1),%eax # %rax = 2%rax 0x0000000000401007 <+57>: add $0x8,%rsp 0x000000000040100b <+61>: retq
在func4里推了一推,发现7满足要求,所以答案可以为7 0
看了下知乎大佬@Yannick 逆向出来的C代码,发现答案不止一个
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 int func4 (int a, int b, int c) { int return_v = c - b; int t = ((unsigned )return_v) >> 31 ; return_v = (t + return_v) >> 1 ; t = return_v + b; if (t - a <= 0 ){ return_v = 0 ; if (t - a >= 0 ){ return return_v; }else { b = t + 1 ; int r = func4(a,b,c); return 2 * r + 1 ; } } else { c = t - 1 ; int r = func4(a, b, c); return 2 *r; } } int func4 (int x, int y, int z) { int k = z - y; k = ((int )(((unsigned )k>>31 ) + k) >> 1 ) + y; if (k < x) return 2 *func4(x, k+1 , z)+1 ; else if (k > x) return 2 *func4(x, y, k-1 ); else return 0 ; }
我们可以发现其实第一个数的取值范围是[0,0xe],我们可以对它进行一个穷举:
1 2 3 4 5 6 7 8 9 10 int main () { for (int i = 0 ; i <= 14 ; i++) if (!func4(i, 0 , 14 )) printf ("%d\n" , i); }
所以最终答案是:
进入phase_5,首先查看phase5的汇编代码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 Dump of assembler code for function phase_5: => 0x0000000000401062 <+0>: push %rbx 0x0000000000401063 <+1>: sub $0x20,%rsp #堆栈相关 0x0000000000401067 <+5>: mov %rdi,%rbx # rbx = rdi 0x000000000040106a <+8>: mov %fs:0x28,%rax # 将内存中一段数据移到rax 0x0000000000401073 <+17>: mov %rax,0x18(%rsp) # rax = (rsp + 24) 0x0000000000401078 <+22>: xor %eax,%eax 0x000000000040107a <+24>: callq 0x40131b <string_length> 0x000000000040107f <+29>: cmp $0x6,%eax # 输入的字符串长度为6 0x0000000000401082 <+32>: je 0x4010d2 <phase_5+112> 0x0000000000401084 <+34>: callq 0x40143a <explode_bomb> 0x0000000000401089 <+39>: jmp 0x4010d2 <phase_5+112> # 循环,作用为将读入的字符串取二进制后四位作为偏移量,从0x4024b0处偏移取出字符,然后压入堆栈 { 0x000000000040108b <+41>: movzbl (%rbx,%rax,1),%ecx # ecx = rax+rbx = rax 0x000000000040108f <+45>: mov %cl,(%rsp) # (rsp) = ecx 0x0000000000401092 <+48>: mov (%rsp),%rdx # rdx = rsp 0x0000000000401096 <+52>: and $0xf,%edx # 取edx二进制的后四位 0x0000000000401099 <+55>: movzbl 0x4024b0(%rdx),%edx # edx = rdx+0x4024b0 0x00000000004010a0 <+62>: mov %dl,0x10(%rsp,%rax,1) # rsp+rax+10 = rdx 0x00000000004010a4 <+66>: add $0x1,%rax # rax += 1 0x00000000004010a8 <+70>: cmp $0x6,%rax 0x00000000004010ac <+74>: jne 0x40108b <phase_5+41> # rax!=6时循环 } 0x00000000004010ae <+76>: movb $0x0,0x16(%rsp) 0x00000000004010b3 <+81>: mov $0x40245e,%esi 0x00000000004010b8 <+86>: lea 0x10(%rsp),%rdi 0x00000000004010bd <+91>: callq 0x401338 <strings_not_equal> 0x00000000004010c2 <+96>: test %eax,%eax 0x00000000004010c4 <+98>: je 0x4010d9 <phase_5+119> 0x00000000004010c6 <+100>: callq 0x40143a <explode_bomb> 0x00000000004010cb <+105>: nopl 0x0(%rax,%rax,1) 0x00000000004010d0 <+110>: jmp 0x4010d9 <phase_5+119> 0x00000000004010d2 <+112>: mov $0x0,%eax # eax = 0 0x00000000004010d7 <+117>: jmp 0x40108b <phase_5+41> 0x00000000004010d9 <+119>: mov 0x18(%rsp),%rax 0x00000000004010de <+124>: xor %fs:0x28,%rax 0x00000000004010e7 <+133>: je 0x4010ee <phase_5+140> 0x00000000004010e9 <+135>: callq 0x400b30 <__stack_chk_fail@plt> 0x00000000004010ee <+140>: add $0x20,%rsp 0x00000000004010f2 <+144>: pop %rbx 0x00000000004010f3 <+145>: retq
可以看到这段代码的逻辑是取出输入的字符的二进制后四位作为偏移量,从0x4024b0处偏移此偏移量取出字符,然后压入堆栈,再到后面的循环中从第一个压入的堆栈与地址$0x40245e中所含的字符进行比较,先打印0x4024b0处的字符:
1 2 (gdb) x/s 0x4024b0 0x4024b0 <array.3449>: "maduiersnfotvbylSo you think you can stop the bomb with ctrl-c, do you?"
再打印$0x40245e中的字符:
1 2 (gdb) x/s 0x40245e 0x40245e: "flyers"
由此可知我们只要让输入的6个字符的ascii码的后四位作为偏移量,在maduiersnfotvbyl这十六个字符中偏移正确的值,最后取出flyers 就可以了,flyers 对应的偏移量为 9fe567
所以我们的答案就很显然了,在Terminal中使用man ascii语句查看所有字符对应的ascii码,找出正确偏移的字符,得到一组可行的答案:9?>567
phase_6的代码就有点长了
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 00000000004010f4 <phase_6>: 4010f4: 41 56 push %r14 4010f6: 41 55 push %r13 4010f8: 41 54 push %r12 4010fa: 55 push %rbp 4010fb: 53 push %rbx 4010fc: 48 83 ec 50 sub $0x50,%rsp 401100: 49 89 e5 mov %rsp,%r13 401103: 48 89 e6 mov %rsp,%rsi 401106: e8 51 03 00 00 callq 40145c <read_six_numbers> 40110b: 49 89 e6 mov %rsp,%r14 # r14 = rsp[0] 40110e: 41 bc 00 00 00 00 mov $0x0,%r12d # r12d = 0 # 循环体2 r13每次+4,r12每次+1直到r12 = 6 { 401114: 4c 89 ed mov %r13,%rbp # rbp = r13 401117: 41 8b 45 00 mov 0x0(%r13),%eax # eax = r13+0x0 40111b: 83 e8 01 sub $0x1,%eax # eax-- 40111e: 83 f8 05 cmp $0x5,%eax # 小于等于5时不爆炸 401121: 76 05 jbe 401128 <phase_6+0x34> 401123: e8 12 03 00 00 callq 40143a <explode_bomb> 401128: 41 83 c4 01 add $0x1,%r12d # r12d += 1 40112c: 41 83 fc 06 cmp $0x6,%r12d 401130: 74 21 je 401153 <phase_6+0x5f> # r12d是否等于6 401132: 44 89 e3 mov %r12d,%ebx # ebx = r12d # 循环体1,作用为读入堆栈上的第2-6个数字,和第1个数字相比,如果相同就爆炸 { 401135: 48 63 c3 movslq %ebx,%rax # rax = ebx 401138: 8b 04 84 mov (%rsp,%rax,4),%eax # 读入堆栈上第rax个数放到eax上 40113b: 39 45 00 cmp %eax,0x0(%rbp) 40113e: 75 05 jne 401145 <phase_6+0x51> # eax 为rbp的第0个数时 爆炸 401140: e8 f5 02 00 00 callq 40143a <explode_bomb> 401145: 83 c3 01 add $0x1,%ebx # ebx += 1 401148: 83 fb 05 cmp $0x5,%ebx 40114b: 7e e8 jle 401135 <phase_6+0x41> # 小于等于5跳转 } 40114d: 49 83 c5 04 add $0x4,%r13 # r13 += 4 401151: eb c1 jmp 401114 <phase_6+0x20> } 401153: 48 8d 74 24 18 lea 0x18(%rsp),%rsi # rsi = rsp[6] 401158: 4c 89 f0 mov %r14,%rax # rax = r14 = *rsp[0] 40115b: b9 07 00 00 00 mov $0x7,%ecx # ecx = 7 # 循环体3, 对输入的每个数进行 a[i] = 7 - a[i]操作 { 401160: 89 ca mov %ecx,%edx # edx = 7 401162: 2b 10 sub (%rax),%edx # edx -= rax 401164: 89 10 mov %edx,(%rax) # (rax) = 7-rsp[0] 401166: 48 83 c0 04 add $0x4,%rax # rax += 4 40116a: 48 39 f0 cmp %rsi,%rax 40116d: 75 f1 jne 401160 <phase_6+0x6c> # 循环直到 rax == rsp[0] } 40116f: be 00 00 00 00 mov $0x0,%esi # esi = 0 401174: eb 21 jmp 401197 <phase_6+0xa3> # 循环体4,rsi == 24时跳出 { # 循环5,ecx == eax 跳出//即eax == 7 跳出 { 401176: 48 8b 52 08 mov 0x8(%rdx),%rdx # rdx = (rdx所存地址+8) 40117a: 83 c0 01 add $0x1,%eax # eax += 1 40117d: 39 c8 cmp %ecx,%eax 40117f: 75 f5 jne 401176 <phase_6+0x82> # ecx = eax } 401181: eb 05 jmp 401188 <phase_6+0x94> # 循环体6,ecx > 1 跳出 { 401183: ba d0 32 60 00 mov $0x6032d0,%edx # edx = 0x6032d0 401188: 48 89 54 74 20 mov %rdx,0x20(%rsp,%rsi,2) # rsp + 0x20 + 2rsi = rdx 40118d: 48 83 c6 04 add $0x4,%rsi # rsi += 4 401191: 48 83 fe 18 cmp $0x18,%rsi 401195: 74 14 je 4011ab <phase_6+0xb7> # rsi == 24 401197: 8b 0c 34 mov (%rsp,%rsi,1),%ecx # ecx = rsp[rsi] 40119a: 83 f9 01 cmp $0x1,%ecx 40119d: 7e e4 jle 401183 <phase_6+0x8f> # ecx <= 1 } 40119f: b8 01 00 00 00 mov $0x1,%eax # eax = 1 4011a4: ba d0 32 60 00 mov $0x6032d0,%edx # edx = 0x6032d0 4011a9: eb cb jmp 401176 <phase_6+0x82> } 4011ab: 48 8b 5c 24 20 mov 0x20(%rsp),%rbx # rbx = rsp[8] 4011b0: 48 8d 44 24 28 lea 0x28(%rsp),%rax # rax = rsp[9] 4011b5: 48 8d 74 24 50 lea 0x50(%rsp),%rsi # rax = rsp[20] 4011ba: 48 89 d9 mov %rbx,%rcx # rcx = rbx # 循环7,循环直到rsi == rax { 4011bd: 48 8b 10 mov (%rax),%rdx # rdx = rax 4011c0: 48 89 51 08 mov %rdx,0x8(%rcx) # (rcx+8) = rax 4011c4: 48 83 c0 08 add $0x8,%rax # rax += 8 4011c8: 48 39 f0 cmp %rsi,%rax 4011cb: 74 05 je 4011d2 <phase_6+0xde> 4011cd: 48 89 d1 mov %rdx,%rcx 4011d0: eb eb jmp 4011bd <phase_6+0xc9> } 4011d2: 48 c7 42 08 00 00 00 movq $0x0,0x8(%rdx) # (rdx + 8) = 0 4011d9: 00 4011da: bd 05 00 00 00 mov $0x5,%ebp # ebp = 5 # 循环8 循环直到ebp < 0 { 4011df: 48 8b 43 08 mov 0x8(%rbx),%rax # rax = (rbx + 8) 4011e3: 8b 00 mov (%rax),%eax # eax = (rax) 4011e5: 39 03 cmp %eax,(%rbx) 4011e7: 7d 05 jge 4011ee <phase_6+0xfa> # 如果 rbx < eax,爆炸 4011e9: e8 4c 02 00 00 callq 40143a <explode_bomb> 4011ee: 48 8b 5b 08 mov 0x8(%rbx),%rbx # rbx = (rbx + 8) 4011f2: 83 ed 01 sub $0x1,%ebp # ebp-- 4011f5: 75 e8 jne 4011df <phase_6+0xeb> } 4011f7: 48 83 c4 50 add $0x50,%rsp 4011fb: 5b pop %rbx 4011fc: 5d pop %rbp 4011fd: 41 5c pop %r12 4011ff: 41 5d pop %r13 401201: 41 5e pop %r14 401203: c3 retq
1 2 3 4 5 6 7 (gdb) x/24w 0x6032d0 0x6032d0 <node1>: 332 1 6304480 0 0x6032e0 <node2>: 168 2 6304496 0 0x6032f0 <node3>: 924 3 6304512 0 0x603300 <node4>: 691 4 6304528 0 0x603310 <node5>: 477 5 6304544 0 0x603320 <node6>: 443 6 0 0
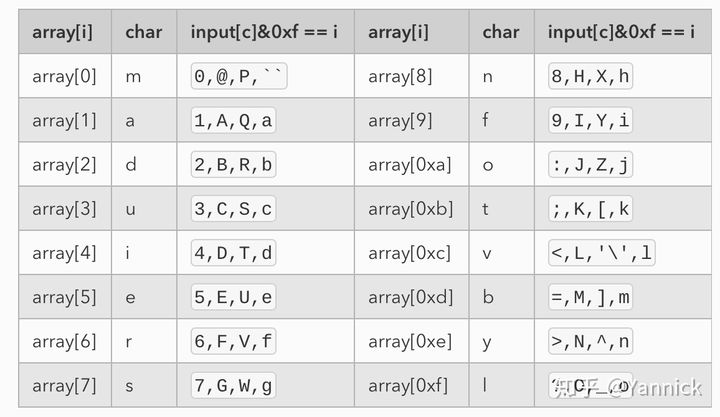
可以看出来前面的代码要求我们输入的数字都不一样且小于等于6,然后它里面有有个链表需要我们进行比较,我们输入的数字的顺序就是比较链表节点的顺序,而其中有个判断又需要我们将比较的这些链表中的数据降序输出,带入数字推断后得到期望的顺序3 4 5 6 1 2,每位都与7取余后得到答案: 4 3 2 1 6 5
写的很简陋,详细的分析建议看大佬的Introduction to CSAPP(十九):这可能是你能找到的分析最全的Bomblab了
在看bomb文件的反汇编代码的时候,看到了个secret_phase全局搜索后在phase_defuse中发现了调用
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 00000000004015c4 <phase_defused>: 4015c4: sub $0x78,%rsp 4015c8: mov %fs:0x28,%rax 4015cf: 4015d1: mov %rax,0x68(%rsp) 4015d6: xor %eax,%eax 4015d8: cmpl $0x6,0x202181(%rip) # 603760 <num_input_strings> 4015df: jne 40163f <phase_defused+0x7b> 4015e1: lea 0x10(%rsp),%r8 4015e6: lea 0xc(%rsp),%rcx 4015eb: lea 0x8(%rsp),%rdx 4015f0: mov $0x402619,%esi # 这里包括下面发现了奇怪的地址,打印看看,发现是 "%d %d %s" 4015f5: mov $0x603870,%edi # 这里是 "" 4015fa: callq 400bf0 <__isoc99_sscanf@plt> 4015ff: cmp $0x3,%eax # sscanf的返回值表示输入的参数个数,如果是3个,就到401604行,那么究竟什么时候会执行这段逻辑呢? 401602: jne 401635 <phase_defused+0x71> 401604: mov $0x402622,%esi # "DrEvil" 401609: lea 0x10(%rsp),%rdi # 比较 "DrEvil" 和某个值 40160e: callq 401338 <strings_not_equal> 401613: test %eax,%eax 401615: jne 401635 <phase_defused+0x71> 401617: mov $0x4024f8,%edi # "Curses, you've found the secret phase!" 40161c: callq 400b10 <puts@plt> # 打印之 401621: mov $0x402520,%edi # "But finding it and solving it are quite different..." 401626: callq 400b10 <puts@plt> # 打印之 40162b: mov $0x0,%eax 401630: callq 401242 <secret_phase> # 调用了彩蛋关 401635: mov $0x402558,%edi # "Congratulations! You've defused the bomb!" 40163a: callq 400b10 <puts@plt> # 打印之 40163f: mov 0x68(%rsp),%rax 401644: xor %fs:0x28,%rax 40164b: 40164d: je 401654 <phase_defused+0x90> 40164f: callq 400b30 <__stack_chk_fail@plt> 401654: add $0x78,%rsp 401658: retq 401659: nop 40165a: nop 40165b: nop 40165c: nop 40165d: nop 40165e: nop 40165f: nop
阅读后发现在前面某个关卡处输入的秘文为整数 整数 字符串时进入secret,推测字符串为前文发现的DrEvil,又发现只有phase4和phase3能满足这个要求,然后都尝试后发现在phase4输入的秘文后接一个DrEvil可以进入隐藏的secret_phase,以下为secret_phase的源码:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 0000000000401242 <secret_phase>: 401242: push %rbx 401243: callq 40149e <read_line> 401248: mov $0xa,%edx 40124d: mov $0x0,%esi 401252: mov %rax,%rdi 401255: callq 400bd0 <strtol@plt> 40125a: mov %rax,%rbx # 断点可以设置在这里,打印后发现,rax中存的是我们输入的值 40125d: lea -0x1(%rax),%eax # eax = eax - 1 401260: cmp $0x3e8,%eax # eax - 0x3e8 <= 0 即 in - 1 <= 1000 401265: jbe 40126c <secret_phase+0x2a> 401267: callq 40143a <explode_bomb> # 不满足时 爆炸 40126c: mov %ebx,%esi # 这个是我们输入的值 40126e: mov $0x6030f0,%edi # 观察输入的参数: # (gdb) x 0x6030f0 # 0x6030f0 <n1>: 0x00000024 401273: callq 401204 <fun7> 401278: cmp $0x2,%eax 40127b: je 401282 <secret_phase+0x40> # fun7返回值和2比,如果等于零,则成功 40127d: callq 40143a <explode_bomb> 401282: mov $0x402438,%edi 401287: callq 400b10 <puts@plt> 40128c: callq 4015c4 <phase_defused> 401291: pop %rbx
关键点就在于func7这个函数了:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 0000000000401204 <fun7>: # %esi 存我们输入的值 # %edi 存某一地址 401204: sub $0x8,%rsp 401208: test %rdi,%rdi # 查看是否为null 40120b: je 401238 <fun7+0x34> # 满足跳转 40120d: mov (%rdi),%edx 40120f: cmp %esi,%edx 401211: jle 401220 <fun7+0x1c> 401213: mov 0x8(%rdi),%rdi 401217: callq 401204 <fun7> 40121c: add %eax,%eax 40121e: jmp 40123d <fun7+0x39> 401220: mov $0x0,%eax 401225: cmp %esi,%edx 401227: je 40123d <fun7+0x39> 401229: mov 0x10(%rdi),%rdi 40122d: callq 401204 <fun7> 401232: lea 0x1(%rax,%rax,1),%eax 401236: jmp 40123d <fun7+0x39> 401238: mov $0xffffffff,%eax # 返回全1序列 40123d: add $0x8,%rsp 401241: retq
大佬@Yannick 逆向的等价C语言:
1 2 3 4 5 6 7 8 9 10 11 12 13 int fun7 (int cmp, Node* addr) { if (addr == 0 ){ return -1 ; } int v = addr->value; if (v == cmp){ return 0 ; }else if ( v < cmp){ return 1 + 2 *fun7(cmp, addr->right); }else { return 2 *func7(cmp, addr->left); } }
查看这个二叉树:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 (gdb) x/120 0x6030f0 0x6030f0 <n1>: 36 0 6304016 0 0x603100 <n1+16>: 6304048 0 0 0 0x603110 <n21>: 8 0 6304144 0 0x603120 <n21+16>: 6304080 0 0 0 0x603130 <n22>: 50 0 6304112 0 0x603140 <n22+16>: 6304176 0 0 0 0x603150 <n32>: 22 0 6304368 0 0x603160 <n32+16>: 6304304 0 0 0 0x603170 <n33>: 45 0 6304208 0 0x603180 <n33+16>: 6304400 0 0 0 0x603190 <n31>: 6 0 6304240 0 0x6031a0 <n31+16>: 6304336 0 0 0 0x6031b0 <n34>: 107 0 6304272 0 0x6031c0 <n34+16>: 6304432 0 0 0 0x6031d0 <n45>: 40 0 0 0 0x6031e0 <n45+16>: 0 0 0 0 0x6031f0 <n41>: 1 0 0 0 0x603200 <n41+16>: 0 0 0 0 0x603210 <n47>: 99 0 0 0 0x603220 <n47+16>: 0 0 0 0 0x603230 <n44>: 35 0 0 0 0x603240 <n44+16>: 0 0 0 0 0x603250 <n42>: 7 0 0 0 0x603260 <n42+16>: 0 0 0 0 0x603270 <n43>: 20 0 0 0 0x603280 <n43+16>: 0 0 0 0 0x603290 <n46>: 47 0 0 0 0x6032a0 <n46+16>: 0 0 0 0 0x6032b0 <n48>: 1001 0 0 0 0x6032c0 <n48+16>: 0 0 0 0
画出其结构:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 └─ 36 ├─ 8 │ ├─ 6 │ │ ├─ left: 1 │ │ └─ right: 7 │ └─ 22 │ ├─ left: 20 │ └─ right: 35 └─ 50 ├─ 45 │ ├─ left: 40 │ └─ right: 47 └─ 107 ├─ left: 99 └─ right: 1001
然后我就穷举了。。。
得到的答案是22或者20,终于拆外所有炸弹
【读厚 CSAPP】II Bomb Lab
Introduction to CSAPP(十九):这可能是你能找到的分析最全的Bomblab了